The security password is 'constant vigilance'
Charles Henderson has seen the dark side of the Internet - he works there, you might say, as director of application security services for SpiderLabs, the "advanced security team" at Trustwave, a leading data-security firm.
Charles Henderson has seen the dark side of the Internet - he works there, you might say, as director of application security services for SpiderLabs, the "advanced security team" at Trustwave, a leading data-security firm.
But ask Henderson about the latest risks facing companies and consumers, and he soon starts talking about a seemingly lighter subject: a pregnant woman who works at a Fortune 500 company.
Henderson will only call her "Sarah." He can't use her actual name because of client confidentiality. But he says he saw virtually the identical story play out half a dozen times last year as SpiderLabs investigated about 220 corporate security breaches and consulted with thousands of other security clients.
As anyone would be, Sarah was thrilled to be expecting, and shared her excitement on a social-networking site. Henderson won't name names there, either, but you can go ahead and guess.
That was pretty much all the attacker needed. He soon sent out a message labeled "Sarah's baby pictures," and many of her friends and coworkers enthusiastically downloaded his malicious code. That made them victims of a scam known as "spear-phishing," a targeted version of the more familiar phishing scam in which the bait is a broad-based e-mail telling recipients that something has gone wrong with one of their accounts.
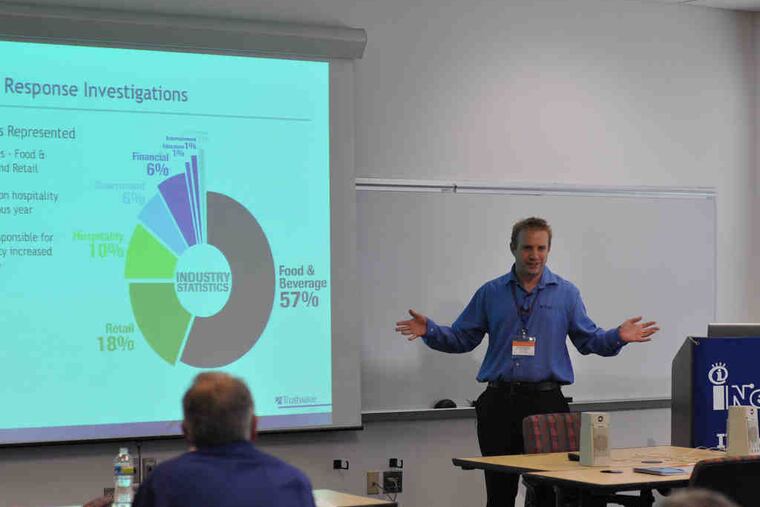
Just like the old Tom and Jerry cartoons, the cat-and-mouse game of hacker vs. IT professional never ends but continually changes scenes, though with anything but humorous stakes. That's why Henderson and other security experts drew an avid crowd of about 75 potential victims to a "Data Security Summit" on Wednesday at Penn State's Great Valley campus.
The all-day session was sponsored by INetU Inc., an Allentown Web-hosting company that also runs server farms in Chicago and Amsterdam. Other speakers included Microsoft's Hameed Mohammed, an expert in cloud-computing security who likens today's frequent data breaches to the relatively high level of air and auto accidents that occurred in the 1950s, when jets and superhighways were likewise in their infancy.
Henderson and Mohammed both aimed their advice at businesses trying to secure their systems and networks. But computer users of any type can benefit from warnings gleaned from their work.
Mohammed shared a vivid illustration of the importance of "strong passwords," with help from an interactive tool developed by Mandylion Research Labs that shows how many hours - or minutes - of brute-force, check-every-combination computing power are necessary to crack a weak or stronger password.
He checks one attendee's password: six letters, with one capital, and one number. Mandylion says that generates three billion combinations - impressive until Mohammed notes the result: A single computer could crack it in less than six minutes.
Add two letters, and the number of combinations jumps to two trillion. That would take a single computer 60 hours to crack - a lot for one "evil guy," as Mohammed puts it, but less than 15 minutes' work for an "evil gang" running 250 computers.
But add two special characters to it - say, an & and an = - and the number of possibilities jumps to two quadrillion. Cracking that password with brute force would take a single computer 62,000 hours - which explains why they're called "strong."
For his part, Henderson eagerly awaits the day when passwords are a thing of the past, replaced by better alternatives such as "two-factor authentication."
Till then, Henderson's suggestion is to avoid reusing the same password, a practice that exposes users to repeated damage from a single security breach. If a hacker obtains your name and a password you use for multiple purposes, you're in hot water.
Henderson also warns that consumers have an odd tendency to be lulled - or perhaps just overly wowed - by the latest gizmos. "When they get a new technology that they're not familiar with, they trust it more," he says.
The sad truth is that the battle with malware will continue for a long time, and some of the odds are in the bad guys' favor. "An attacker only needs to find one hole," he says. "A defender has to plug all the holes."